Why ModSecurity Should Be Your Web Application Firewall
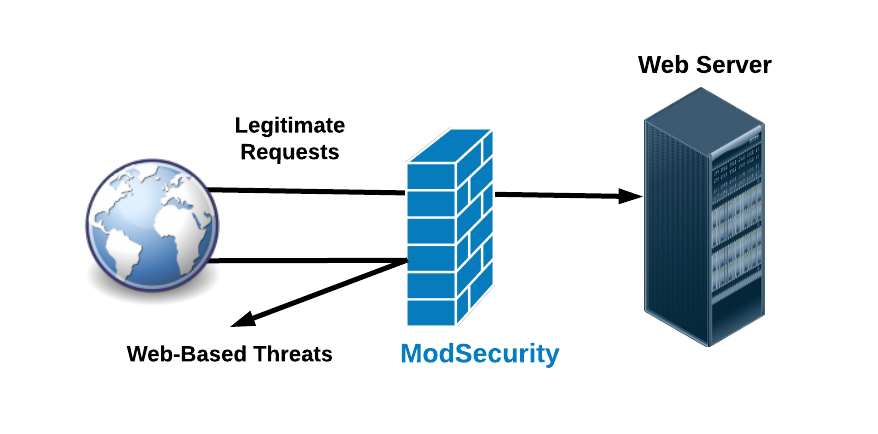
ModSecurity helps to protect your site from a variety of attacks by matching up known attack patterns and identifying anomalies. Here’s what you need to know about the web application firewall and how it protects you.
What Is ModSecurity?
ModSecurity is a web application firewall designed to protect against web-based threats (we’ll come back to these later), including:
- Brute-force attacks
- SQL injection
- cross-site scripting
ModSecurity works by detecting and blocking requests that match signatures of known attack patterns and/or through the use of anomaly scoring. On occasion, ModSecurity may misinterpret a legitimate user’s actions as a threat. Such users will usually encounter a 403 “Forbidden” HTTP status code.
Finding The Issue
The first step to identifying mis-sent 403’s is investigating your website’s error logs. If these logs indicate your site blocked a legitimate request, ModSecurity may be the cause. Resolving the issue is usually a matter of confirming the blocked request was indeed legitimate, then either adding a whitelist or adjusting ModSecurity’s ruleset to prevent it from blocking similar legitimate requests in the future.
If we host your website, and you don’t have the time or resources to investigate, our support team can do it for you. Just open a ticket through the Client Portal, and we can examine your logs, determine the cause, and apply one of our application-specific rulesets. These rulesets help ModSecurity better recognize legitimate users, and include Magento, WordPress, and other platforms featured on our website.
Brute-Force Attacks
Brute-force attacks attempt to access your site’s admin panel with fast, repeated attempts to guess the password. This method follows a consistent pattern. First, the password is entered into the login form, then sent to the server. If the attack succeeds, the server rejects the password, and content management system (CMS, like Magento, WordPress, and so on) returns an unauthorized token, which redirects the user to the login page. Brute force attacks repeat these login attempts at a furious pace and continue until they succeed, or are detected and stopped.
When the web server notices a high rate of failed logins, ModSecurity blocks the IP address attempting to log in. However, our settings require a relatively high number of failed password entries before perceiving those attempts as a brute force attack. If you are a legitimate user struggling with a password, you will come nowhere near this threshold.
SQL Injection
ModSecurity uses a similar technique to derail SQL injection, a common form of attack that attempts to exploit vulnerabilities in an application to insert a malicious SQL statement into your database. These statements normally run automatically as part of database operation. If successful, these attacks can change or disclose your data without your knowledge, or even destroy such data.
SQL injection usually inserts these statements into entry fields, such as those requesting usernames or passwords, and require a security vulnerability that allows user input to be unexpectedly executed as an SQL statement. While the technical details are beyond the scope of this entry, it’s enough to know that ModSecurity resists these nefarious activities.
Cross-Site Scripting (XSS)
In cross-site scripting (XSS), malicious users inject scripts into the HTML of vulnerable websites. When an unsuspecting user clicks the compromised content, the script gains all permissions attached to that user’s system. With this method, attackers can learn login credentials, upload viruses, and even gain administrative access.
ModSecurity intervenes by detecting and blocking requests that attempt to exploit this class of vulnerabilities.
ModSecurity Alone Isn’t Enough
Like any security system, ModSecurity cannot credibly claim perfection. It will, however, make you a harder target. Combined with other best practices like prompt installation of your application’s security patches, a strong password policy, cautious deployment of plug-ins, and two-factor authentication for admin access, ModSecurity plays a key role protecting your website.
For help getting the most of ModSecurity, or for general inquiries, please contact our 24/7 Support Team by email or through your Client Portal.
Posted in:
Hostdedi