How to Use Keyword Research to Drive Your Content Marketing
If you own a small business and want your store to be found online via Google and other search engines, you’ll need to do keyword research. Keyword research is core to knowing both what is being searched for and what resonates with your audience. It also helps to construct resonant and valuable product descriptions, content marketing assets, and more.
As you build out your content marketing strategy for 2020, it’s important that you align your content with high-value, high-intent keywords. By doing so, you’re able to drive revenue and secure brand recognition in the locations your consumers are visiting.
Following these best practices allows you to step into content marketing with the confidence that your audience (and ultimately, your shoppers) will take a greater interest in what you have to say, and that Google will boost your site in its search rankings.
Learn more about how to optimize your Ecommerce SEO.
What Is Keyword Research?
Keyword research is how you identify the keywords your target customers are using to search online for what you’re offering. If you sell toys for babies and toddlers for example, your keywords are what parents and others shopping for kids’ toys type into the search bar (“safe toys for a 1-year-old” or “baby teething toys”).
As you do your keyword research, you’ll pull together a list of keywords to rank in search engine results. Customers use Google and other search engines to locate websites based on the questions they’re trying to answer or products they’re looking to purchase online.
Searches can include keywords or keyphrases. Simply put, these are the terms your customers type into the search bar.
Here are some essential keyword terms and metrics to know.
Keyword
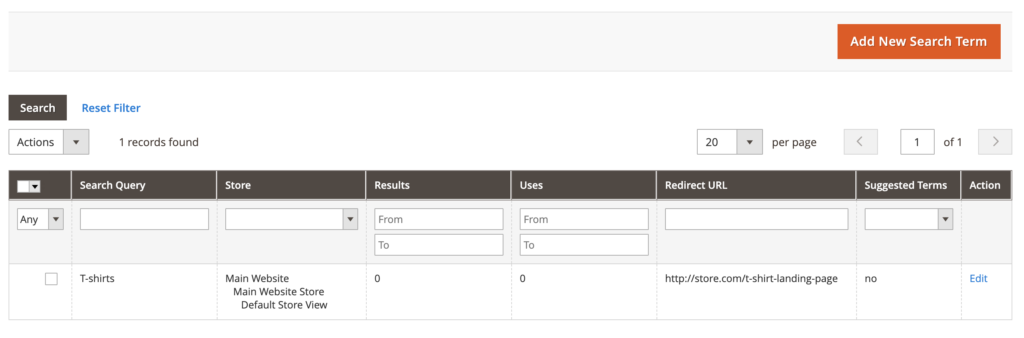
A keyword is a specific word searchers type into a search engine (or say to a search engine). Keywords can be tracked, charted, and measured to show what people are looking for when using search engines. They may search for “infant T-shirts” or “minivan air filters.” And yes, a keyword can (and often does) have multiple words.
Keyphrases and Long-Tail Keywords
A keyword is usually sentence-length or a sentence fragment. Keyphrases and long-tail keywords are essentially the same concept, and are much more highly specific and specialized. For instance, “orange baby tees” might be a keyphrase while “where to buy baby tees in NYC” could be a long-tail keyword.
Keyword Volume
Keyword volume is the average number of monthly searches for any given keyword. The higher the volume is for a given keyword, the more popular and valuable that keyword is. Advertisers and businesses trying to place in the search engine results pages (SERP) rankings usually want the highest volume keywords.
There’s a big exception, though, to the idea that all keywords must have high volumes — niche keywords often have lower volumes, as do long-tail keywords, but they can still be very desirable if they attract a valuable audience to your website.
Keyword Difficulty and Competition
Keyword difficulty tells you how challenging it is to rank high on the SERPs for a particular keyword. If a word is highly competitive, you may be better off choosing different keywords to emphasize in your content marketing. A larger number means a keyword is more competitive while a keyword with a lower difficulty number will be easier to rank for.
CPC (Cost per Click)
CPC is the price a search engine advertiser pays for a visitor’s click on the ad. Search engines offer advertising and typically use a CPC model to charge for the service. These ads are typically shown at the top of the search results, and are clearly marked as an ad. Every click charges against the accounts that advertisers hold with the search engine’s company. For instance, you can advertise with Google and pay for every individual click to your ads. The more competitive the keyword, the higher the cost per click.
Cost-Per-Click (CPC) is the amount search engine advertisers pay when someone clicks their ad.
Putting It All Together: Using Keyword Metrics
Keyword and keyphrase research give you a glimpse into what your customers are looking for online so you can position your content accordingly. For content marketing, this provides shop owners with greater insight into what questions, goals, and desires customers have.
Volume, competition, and CPC information helps you identify the desirable words. The higher the volume, competition, and CPC, the more valuable a search term typically is for you (and your competitors).
Once you have your keyword list, you can start planning your content. This is the keyword strategy part of your content marketing.
How to Do Keyword Research
Online research tools for finding the right keywords and keyphrases can show you how common search terms are used, what related keywords they’re also searching for, and how you can connect these searches to specific content plans for your content marketing.
Step One: Use Search Intent to Create a Keyword List to Research
If you don’t know what questions your website visitors are asking, it’s hard to know what keywords will actually increase traffic. Start with a list of questions your audience is trying to answer. The answer to these questions should ultimately be related to your product. If you can’t think of any questions, start with a few words associated with your product.
For example, if you sell cabin air filters for cars, trucks, and other consumer vehicles, your potential customers may be asking or thinking
- Can I change my cabin air filter myself?
- Where can I find air filters for a Toyota Camry?
- What’s the right air filter for my vehicle?
- Who has the cheapest car air filters?
- What does a cabin air filter cost?
- How do I know if a car air filter is dirty?
- How often should you change your air filter?
Write down keywords and keyphrases that naturally result from these questions. It’s also okay to have several hundred keywords. In fact, a typical business should rank for as many relevant keywords as possible. For example, “Where can I find air filters for a Toyota Camry?” could be expanded to dozens, if not hundreds, of car makes and models.
Step Two: Test and Expand Your Keywords With Keyword Tools
Using a keyword tool, you can prioritize the keywords you use in your content.
Good keywords bring traffic to your site and ultimately result in conversions, or purchases. Relevance is important. If you sell cabin air filters, you don’t want a large volume of traffic from people looking for T-shirts or gardening equipment. Generally speaking, a good keyword for you is highly-relevant for shoppers, has decent volume, fits your product, and is something you can rank for by putting in the effort.
Typically, you at least want to know the volume and the competitiveness of your keywords. High-volume keywords attract marketers — often making these words more competitive. If you’re offering a niche product, it generally means it’s better to have more specific terms even if they don’t attract a ton of traffic. Every keyword search matters when you’re selling a product with niche appeal. According to Moz, keywords that are less competitive and more specific (i.e., long-tail keywords that fit your customers) are 70% better at converting visitors to your website than competitive, major keywords.
You also want to identify similar keywords and start building your content with the right combinations of keywords.
Here are three, free keyword tools to get you started. All provide helpful insights that allow you to shape your content marketing.
Answer The Public
With Answer The Public, you can identify search engine user questions that are closely related to each other. This tool is very helpful if you’re looking for keywords to use with those you already have.
Keywordtool.io
To uncover more long-tail, specific keywords you can use in your marketing, use Keyword Tool. This tool uses Google Autocomplete to find alternative keywords and is free even without an account — though you’ll get a lot more keywords and relevant data with a paid account.
Ubersuggest
The free keyword tool Ubersuggest provides keyword suggestions and competitor research. It can help you understand how difficult it will be to rank for a certain keyword.
As you build your knowledge of keyword research, or start working with larger data sets, you might consider using one of the top paid services: Ahrefs or SEMrush.
Step Three: Plan Your Content
And now, the moment of truth. You have your keywords and you’re ready to begin planning your content. Take your keywords and group them by topic. Create questions based on these keywords that reflect what your customers are really asking. Many keyword tools will actually do this for you.
For instance, if we use the free tool Answer The Public to create questions for “car air filter,” the results are questions and search queries:
- What car air filter do I need?
- Can I wash my car air filter with water?
- How to make a car air filter
- Where to change car air filter
- Does car air conditioning filter smoke
These are related to our keyword and are real questions and problems consumers are trying to answer. They also happen to be good possible topics for new content. You could easily write a blog post for all of these or address the questions on your website.
In this way, eCommerce retailers can quickly and affordably create topic lists using your keywords. If you ever run out of ideas for the content you’re writing, just brainstorm more keywords and see what topics are popular in search.
Step Four: Write Content
From here, use related keywords to fill out the details in your content. If “How to change a car air filter” is your topic, you can use related keywords and questions such as “What car air filter do I need?” and “Where to change a car air filter” as headings and sections. Think about everything your readers would want to know about the topic and try to answer any relevant questions within your content.
Avoid trying to make one single piece of content fit all of your keywords, though. Take care not to confuse being comprehensive with covering all of your SEO bases in one landing page or article. Not only is this a huge turn-off for readers, but too many keywords can reduce the quality of your writing and get your website penalized by search engines. Don’t write only for keyword searches; focus on your readers.
Conclusion
As you analyze your keywords and build your content, don’t be afraid to make course corrections and adjustments. Content marketing requires some experimentation to get right. However, with access to the right tools and information, it’s very possible to get better traction with SEO by using content, and it’s worth putting in the work.
Remember, SEO is more than just keywords. It’s an ecosystem of techniques and strategies designed to make you content as resonant and relevant as it can be. Part of that is ensuring visitors are greeted by an unrivaled user experience that is as quick as it is easy to navigate. Hostdedi Managed hosting makes creating that experience easier with bundled integrations that help to get the most from your content and site.
Learn how Hostdedi Managed WordPress can help and get started today.
The post How to Use Keyword Research to Drive Your Content Marketing appeared first on Hostdedi Blog.





 If the cause is beyond their control—poorly written website code, an unpatched Magento installation, unexpected surges in your site traffic—they can help diagnose the problem and suggest options for resolving it.
If the cause is beyond their control—poorly written website code, an unpatched Magento installation, unexpected surges in your site traffic—they can help diagnose the problem and suggest options for resolving it. With security, you have enough to worry about on your end without wondering whether your hosting provider is holding up theirs. No security system can claim perfection, but consider any of the below to be hosting provider red flags:
With security, you have enough to worry about on your end without wondering whether your hosting provider is holding up theirs. No security system can claim perfection, but consider any of the below to be hosting provider red flags:
 quick-and-painless scalability. Cloud technology makes it easier to allocate extra resources to your service on-demand, as well as provides a cleaner, migration-free path to permanently upgrading (or downgrading) your service.
quick-and-painless scalability. Cloud technology makes it easier to allocate extra resources to your service on-demand, as well as provides a cleaner, migration-free path to permanently upgrading (or downgrading) your service. A stack is a bundle of software designed to run a server. They range in complexity and purpose, and not so long ago a Linux/Apache/MySQL/PHP (LAMP) stack was considered adequate for hosting purposes. As modern web applications have risen to prominence and in complexity, this is no longer the case.
A stack is a bundle of software designed to run a server. They range in complexity and purpose, and not so long ago a Linux/Apache/MySQL/PHP (LAMP) stack was considered adequate for hosting purposes. As modern web applications have risen to prominence and in complexity, this is no longer the case.
 envisioned as the definitive global gathering of the Magento community. MagentoLive serves as a complement to that event, in essence a more “localized” version of Imagine.
envisioned as the definitive global gathering of the Magento community. MagentoLive serves as a complement to that event, in essence a more “localized” version of Imagine. respect and utilize Magento open source community in this effort.
respect and utilize Magento open source community in this effort. 



 If you care enough about PCI compliance to read this article, then you’re on the right track. Following are nine common mistakes for merchants undergoing audit, though your experience may vary according to your business needs and PCI compliance level.
If you care enough about PCI compliance to read this article, then you’re on the right track. Following are nine common mistakes for merchants undergoing audit, though your experience may vary according to your business needs and PCI compliance level. 

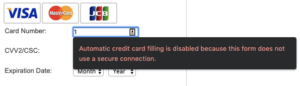
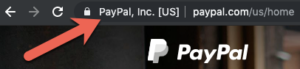
 In ecommerce, PCI is shorthand for Payment Card Industry Data Security Standards (PCI DSS). Created in 2004, PCI DSS aim to help protect consumers and prevent credit card fraud. It is required for any organization that receives, processes, or stores credit card data of any of the five members of the
In ecommerce, PCI is shorthand for Payment Card Industry Data Security Standards (PCI DSS). Created in 2004, PCI DSS aim to help protect consumers and prevent credit card fraud. It is required for any organization that receives, processes, or stores credit card data of any of the five members of the  It is virtually impossible for the typical merchant to be PCI compliant without enlisting the services of a compliant hosting provider. Merchants that host their own websites must meet hosting provider requirements in addition to meeting those for merchants. Such a model works for massive enterprises like Amazon and WalMart, but few others.
It is virtually impossible for the typical merchant to be PCI compliant without enlisting the services of a compliant hosting provider. Merchants that host their own websites must meet hosting provider requirements in addition to meeting those for merchants. Such a model works for massive enterprises like Amazon and WalMart, but few others. 








